Available in editions: CE, BE, SE, SE+, EE
The module lifecycle stage: General Availability
The module has 1 alert.
The module is enabled by default in the Default bundle.
The module is disabled by default in the following bundles: Managed, Minimal.
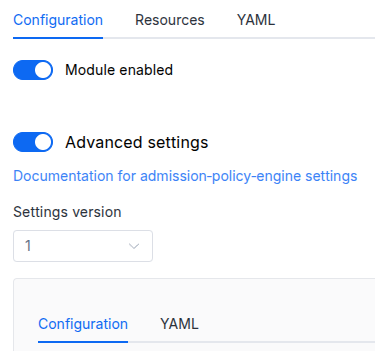
Conversions
The module is configured using the ModuleConfig resource, the schema of which contains a version number. When you apply an old version of the ModuleConfig schema in a cluster, automatic transformations are performed. To manually update the ModuleConfig schema version, the following steps must be completed sequentially for each version :
- Updates from version 1 to 2:
Replace
publishAPI.enablewithpublishAPI.enabled.
Parameters
Schema version: 2
- objectsettings
- objectsettings.controlPlaneConfigurator
Parameters of the
control-plane-managermodule for automatic configuration ofkube-apiserver.- stringsettings.controlPlaneConfigurator.dexCAMode
How to determine the CA that will be used when configuring
kube-apiserver.Custom— use the CA explicitly set via thedexCustomCAparameter (see below). This option comes in handy if you use an external HTTPS load balancer in front of Ingresses, and this load balancer relies on a self-signed certificate.DoNotNeed— a CA is not required (e.g., when using a public LE or other TLS providers).FromIngressSecret— extract the CA of certificate from the Secret that is used in the Ingress. This option comes in handy if you use self-signed certificates with Ingresses.
Default:
DoNotNeedAllowed values:
Custom,DoNotNeed,FromIngressSecret - stringsettings.controlPlaneConfigurator.dexCustomCA
The CA to use if
dexCAModeisCustom. Plain text (no base64). - booleansettings.controlPlaneConfigurator.enabled
Defines if the
control-plane-managermodule should be used to configure OIDC for thekube-apiserver.Default:
true
- booleansettings.highAvailability
Manually enable the high availability mode.
By default, Deckhouse automatically decides whether to enable the HA mode. Click here to learn more about the HA mode for modules.
Examples:
highAvailability: truehighAvailability: false - objectsettings.https
What certificate type to use with Dex/kubeconfig-generator.
This parameter completely overrides the
global.modules.httpssettings.Examples:
https: mode: CustomCertificate customCertificate: secretName: foobarhttps: mode: CertManager certManager: clusterIssuerName: letsencrypt- objectsettings.https.certManager
- stringsettings.https.certManager.clusterIssuerName
What ClusterIssuer to use for Dex/kubeconfig-generator.
Currently,
letsencrypt,letsencrypt-staging,selfsignedare available. Also, you can define your own.Default:
letsencrypt
- objectsettings.https.customCertificate
- stringsettings.https.customCertificate.secretName
The name of the Secret in the
d8-systemnamespace to use with Dex/kubeconfig-generator.This Secret must have the kubernetes.io/tls format.
Default:
false
- stringsettings.https.mode
The HTTPS usage mode:
CertManager— Dex/kubeconfig-generator will use HTTPS and get a certificate from the ClusterIssuer defined in thecertManager.clusterIssuerNameparameter.CustomCertificate— Dex/kubeconfig-generator will use HTTPS using the certificate from thed8-systemnamespace.Disabled— Dex/kubeconfig-generator will work over HTTP only;OnlyInURI— Dex/kubeconfig-generator will work over HTTP (thinking that there is an external HTTPS load balancer in front that terminates HTTPS traffic). All the links in theuser-authnwill be generated using the HTTPS scheme. Load balancer should provide a redirect from HTTP to HTTPS.
Default:
DisabledAllowed values:
Disabled,CertManager,CustomCertificate,OnlyInURI
- stringsettings.idTokenTTL
The TTL of the id token (use
sfor seconds,mfor minutes,hfor hours).It is specified as a string containing the time unit in hours, minutes and seconds: 30m, 20s, 2h30m10s, 24h.
Default:
10mPattern:
^([0-9]+h)?([0-9]+m)?([0-9]+s)?$ - stringsettings.ingressClass
The class of the Ingress controller that will be used for Dex/kubeconfig-generator.
An optional parameter; by default, the
modules.ingressClassglobal value is used.Pattern:
^[a-z0-9]([-a-z0-9]*[a-z0-9])?(\.[a-z0-9]([-a-z0-9]*[a-z0-9])?)*$ - array of objectssettings.kubeconfigGenerator
An array in which additional possible methods for accessing the API server are specified.
This option comes in handy if you prefer not to grant access to the cluster’s API via Ingress but rather do it by other means (e.g., using a bastion host or over OpenVPN).
- stringsettings.kubeconfigGenerator.description
A couple of words how this authentication method differs from others.
- stringsettings.kubeconfigGenerator.id
Required value
The name of the method for accessing the API server (no spaces, lowercase letters).
Pattern:
^[\@\.\:0-9a-z._-]+$ - stringsettings.kubeconfigGenerator.masterCA
A CA for accessing the API:
- If the parameter is not set, Kubernetes CA is used.
- We recommend using a self-signed certificate (and specify it as masterCA) if an HTTP proxy (that terminates HTTPS traffic) is used for exposing.
- stringsettings.kubeconfigGenerator.masterURI
Required value
If you plan to use a TCP proxy, then you must configure a certificate on the API server’s side for the TCP proxy address. Suppose your API servers use three different addresses (
192.168.0.10,192.168.0.11, and192.168.0.12) while the client uses a TCP load balancer (say,192.168.0.15). In this case, you have to re-generate the API server certificates:- edit
kubeadm-config:d8 k -n kube-system edit configmap kubeadm-configand add192.168.0.15to.apiServer.certSANs; - save the resulting config:
kubeadm config view > kubeadmconf.yaml; - delete old API server certificates:
mv /etc/kubernetes/pki/apiserver.* /tmp/; - reissue new certificates:
kubeadm init phase certs apiserver --config=kubeadmconf.yaml; - restart the API server’s container:
docker ps -a | grep 'kube-apiserver' | grep -v pause| awk '{print $1}' | xargs docker restart; - repeat this step for all master nodes.
- edit
- objectsettings.nodeSelector
The same as in the Pods’
spec.nodeSelectorparameter in Kubernetes.If the parameter is omitted or
false, it will be determined automatically. - objectsettings.passwordPolicy
Default:
- stringsettings.passwordPolicy.complexityLevel
Password complexity level.
Depending on the complexity level, a password must meet the following minimum requirements:
None: 1 character.Low: 8 characters.Fair: 8 characters, 1 uppercase letter (A–Z), 1 lowercase letter (a–z), 1 digit.Good: 8 characters, 1 uppercase letter (A–Z), 1 lowercase letter (a–z), 1 digit, 1 special character (!@#$%^&*).Excellent: 8 characters, 1 uppercase letter (A–Z), 1 lowercase letter (a–z), 1 digit, 1 special character (!@#$%^&*), no more than 2 identical characters in a row.
Default:
FairAllowed values:
None,Low,Fair,Good,Excellent - objectsettings.passwordPolicy.lockout
Temporary user lockout settings after consecutive failed login attempts.
- stringsettings.passwordPolicy.lockout.lockDuration
Required value
Temporary lockout duration. Can be set in seconds, minutes, hours, or days:
10s,5m,1h,3d.Pattern:
^(?:(?:[1-9]|[1-9][0-9]+)d)?(?:(?:[1-9]|[1-9][0-9]+)h)?(?:(?:[1-9]|[1-9][0-9]+)m)?(?:(?:[1-9]|[1-9][0-9]+)s)?$ - integersettings.passwordPolicy.lockout.maxAttempts
Required value
Number of consecutive failed login attempts after which the user will be temporarily locked out.
- integersettings.passwordPolicy.passwordHistoryLimit
Number of the user’s previous passwords stored in history to prevent their reuse.
Default:
5Allowed values:
0 <= X - objectsettings.passwordPolicy.rotation
Password rotation settings.
- stringsettings.passwordPolicy.rotation.interval
Required value
Time interval after which the password must be changed. Can be set in seconds, minutes, hours or days:
10s,5m,1h,3d.Pattern:
^(?:(?:[1-9]|[1-9][0-9]+)d)?(?:(?:[1-9]|[1-9][0-9]+)h)?(?:(?:[1-9]|[1-9][0-9]+)m)?(?:(?:[1-9]|[1-9][0-9]+)s)?$
- objectsettings.publishAPI
Settings for exposing the API server using Ingress.
- booleansettings.publishAPI.addKubeconfigGeneratorEntry
Setting it to
falsewill remove an entry in kubeconfig-generator.Default:
true - booleansettings.publishAPI.enabled
Setting it to
truewill create an Ingress resource in thed8-user-authnnamespace in the cluster (it exposes the Kubernetes API).Default:
false - objectsettings.publishAPI.https
The HTTPS mode for the API server Ingress.
Examples:
https: mode: SelfSignedhttps: mode: Global global: kubeconfigGeneratorMasterCA: plainstring- objectsettings.publishAPI.https.global
An additional parameter for the
Globalmode.- stringsettings.publishAPI.https.global.kubeconfigGeneratorMasterCA
If there is an external load balancer in front of the Ingress that terminates HTTPS traffic using non-public CA, then you need to specify the CA so it will be included in kubectl-config.
If you are using certificates issued by the
cert-managermodule and Let’s Encrypt in your cluster, you should set an empty string""as the value.Also, you can set the external LB’s certificate itself as a CA if you can’t get the CA that signed it for some reason. Note that after the certificate is updated on the LB, all the previously generated kubeconfigs will stop working.
- stringsettings.publishAPI.https.mode
The mode of issuing certificates for the Ingress resource.
In the
SelfSignedmode, a CA-signed certificate will be issued for the Ingress resource.Use the following command to get the certificate:
d8 k -n d8-user-authn get secrets kubernetes-api-ca-key-pair -oyaml.In the
Globalmode, the policies specified in theglobal.modules.https.modeglobal parameter will be applied. Thus, if the global parameter has theCertManagermode set (withletsencryptas the ClusterIssuer), then the Let’s Encrypt certificate will be issued for the Ingress resource.Default:
SelfSignedAllowed values:
SelfSigned,Global
- stringsettings.publishAPI.ingressClass
The Ingress class that will be used to expose the Kubernetes API via Ingress.
Pattern:
^[a-z0-9]([-a-z0-9]*[a-z0-9])?(\.[a-z0-9]([-a-z0-9]*[a-z0-9])?)*$ - array of stringssettings.publishAPI.whitelistSourceRanges
An array of CIDRs that are allowed to connect to the API server.
- stringElement of the array
Pattern:
^(([0-9]|[1-9][0-9]|1[0-9]{2}|2[0-4][0-9]|25[0-5])\.){3}([0-9]|[1-9][0-9]|1[0-9]{2}|2[0-4][0-9]|25[0-5])(\/(3[0-2]|[1-2][0-9]|[0-9]))?$
- objectsettings.staticUsers2FA
- booleansettings.staticUsers2FA.enabled
Required value
If set to
true, the static users will be required to use two-factor authentication (2FA) when logging in. This option is useful for enhancing security by requiring an additional verification step during the login process.Default:
false - stringsettings.staticUsers2FA.issuerName
The issuer name for the two-factor authentication (2FA) tokens. This name is visible to users in the 2FA application (e.g., Google Authenticator).
Default:
Deckhouse
- array of objectssettings.tolerations
The same as in the Pods’
spec.tolerationsparameter in Kubernetes;If the parameter is omitted or
false, it will be determined automatically.Example:
tolerations: - key: key1 operator: Equal value: value1 effect: NoSchedule- stringsettings.tolerations.effect
- stringsettings.tolerations.key
- stringsettings.tolerations.operator
- integersettings.tolerations.tolerationSeconds
- stringsettings.tolerations.value
The creation of the DexAuthenticator Custom Resource leads to the automatic deployment of oauth2-proxy to your application’s namespace and connecting it to Dex.
Caution! Since using OpenID Connect over HTTP poses a significant threat to security (the fact that Kubernetes API server doesn’t support OICD over HTTP confirms that), this module can only be installed if HTTPS is enabled (to do this, set the https.mode parameter to the value other than Disabled either at the cluster level or in the module).
Caution! When this module is enabled, authentication in all web interfaces will be switched from HTTP Basic Auth to Dex (the latter, in turn, will use the external providers that you have defined). To configure kubectl, go to https://kubeconfig.<modules.publicDomainTemplate>/, log in to your external provider’s account and copy the shell commands to your console.
Caution! The API server requires additional configuration to use authentication for dashboard and kubectl. The control-plane-manager module (enabled by default) automates this process.