The module lifecycle stage: General Availability
The module has requirements for installation
Warning! When changing module network settings, make sure cert-manager issuer and Code module use the same Ingress class.
- Check
spec.network.ingressClassinCodeInstance.- Check Ingress class in cert-manager
Issuer/ClusterIssuersolver configuration.- After switching Ingress class, re-issue certificates if needed.
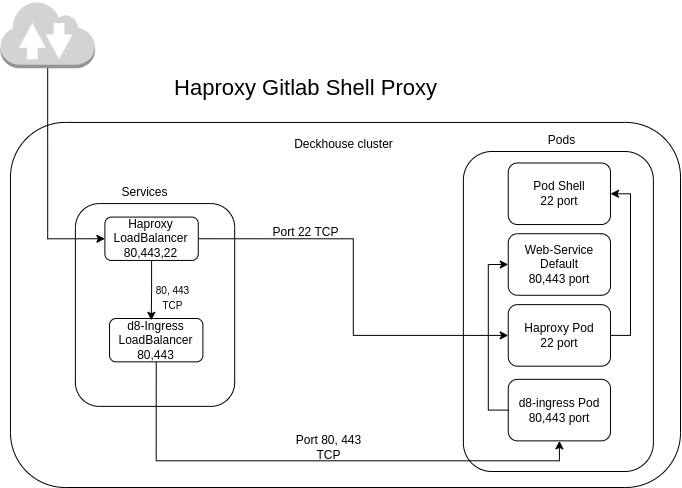
Git SSH Operation on Port 22
By default, the Deckhouse cluster uses the built-in Ingress controller — ingress-nginx. This controller provides access to the web interface (UI) via standard HTTP (port 80) and HTTPS (port 443) ports. However, ingress-nginx does not support TCP port proxying.
To proxy external TCP traffic through port 22 (Git SSH), a special option is provided in the module configuration. When this option is enabled, Haproxy is deployed with a service of type LoadBalancer. Haproxy forwards traffic from port 22 to the corresponding Git SSH Pod. Ports 80 and 443 continue to be handled by ingress-nginx, where TLS traffic termination occurs.
Self-signed certificates (certificates issued with internal Certificate Authority)
To use self-signed certificates in different connections (HTTPS, rediss, SMTPS etc…), create secret or configmap in d8-code namespace with certificates and declare it in CR:
...
spec:
network:
certificates:
customCAs:
- secret: custom-tls-ca
keys:
- ca.crt
- tls.crt
- secret: more-custom-CAs
keys:
- custom-ca-1.crt
- configMap: custom-CA-cm
- configMap: more-custom-CAs-cm
keys:
- custom-ca-2.crt
- custom-ca-3.crt
...Configure custom certificate for web UI
To use your own TLS certificate for the web endpoint, create a TLS Secret in d8-code and reference it in spec.network.web.https.
- Create TLS Secret in
d8-code:
kubectl -n d8-code create secret generic code-web-tls \
--from-file=tls.crt=tls.crt \
--from-file=tls.key=tls.key \
--from-file=ca.crt=ca.crt- Configure
CodeInstanceto use this Secret for web UI and include the certificate innetwork.certificates.customCAsto distribute trust to all containers:
apiVersion: deckhouse.io/v1
kind: CodeInstance
metadata:
name: code
spec:
network:
certificates:
customCAs:
- secret: code-web-tls
keys:
- tls.crt
web:
hostname: code.example.com
https:
mode: CustomCertificate
customCertificate:
secretName: code-web-tlsThe Secret must be in kubernetes.io/tls format and the certificate must be valid for the configured hostname.
If your certificate is signed by a private CA, prefer providing the CA certificate/chain in customCAs.
Features of the ownLoadBalancer option
Warning! ownLoadBalancer DOES NOT support the following modes:
HostPort,HostPortWithSSLPassthrough,HostPortWithProxyProtocol, andHostWithFailover. Ingress-nginx controller modes.
These modes are service exposure modes configured in d8-ingress-nginx IngressNginxController. If your cluster uses one of them, do not enable ownLoadBalancer.
-
Separate IP Address: When the
ownLoadBalancer.enabledoption is enabled for the Code module, a separate IP address is allocated, distinct from the main Deckhouse IP address. A separate DNS record must be created for this address. The following services will be accessible via this DNS record:- Web interface (UI) on ports 80 and 443.
- Git SSH on port 22.
-
Ignored Parameters: When the
ownLoadBalancer.enabledoption is enabled, the following parameters are ignored:spec.network.gitSsh.hostnamespec.network.gitSsh.service.typespec.network.gitSsh.service.nodePort
Instead, the
shellservice is assigned theLoadBalancertype, and Git SSH becomes accessible via the same domain as the web service. -
Default value:
ownLoadBalancer.enabledistrueby default.
Configure ownLoadBalancer.httpBackends
Use spec.network.ownLoadBalancer.httpBackends to explicitly define which IngressNginxController instances receive HTTP(S) traffic from the Code HAProxy LoadBalancer.
- If this list is empty, backend service names are derived automatically from the selected Ingress class.
- Use this option when you run several ingress controllers and want to bind Code traffic to specific controllers.
Example:
apiVersion: deckhouse.io/v1
kind: CodeInstance
metadata:
name: code
spec:
network:
ownLoadBalancer:
enabled: true
httpBackends:
- system-controllerConfiguration Example
Below is an example of enabling Haproxy for Git SSH proxying in CodeInstance:
apiVersion: deckhouse.io/v1
kind: CodeInstance
metadata:
name: code
spec:
...
network:
ownLoadBalancer:
enabled: true
...Verification checklist
After applying changes, verify:
kubectl -n d8-code get svc shell webservice-default- A
LoadBalancerexternal IP is assigned to the expected service(s). - DNS A record points to that external IP.
- Git SSH access works:
ssh -T git@<host> -p 22Haproxy Workflow Diagram
Haproxy inside the Deckhouse cluster operates according to the following diagram: