Available with limitations in: CE, BE, SE, SE+, EE, CSE Lite (1.73), CSE Pro (1.73)
The module lifecycle stage: General Availability
The module has requirements for installation
Requirements
To the Deckhouse version: 1.72 and above.
Parameters
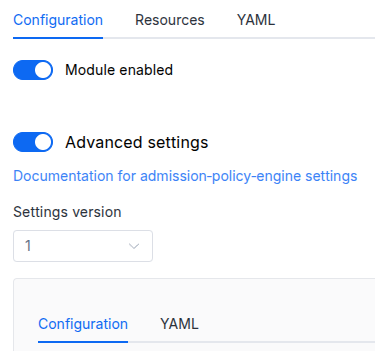
Schema version: 1
-
-
booleansettings.enableAuditLogEnables audit log (EE only feature).
Example:
enableAuditLog: true -
booleansettings.enableUserInterfaceEnables User Interface.
Default:
trueExample:
enableUserInterface: false -
objectsettings.https
What certificate type to use with Stronghold.
This parameter completely overrides the
global.modules.httpssettings.Examples:
customCertificate: secretName: stronghold-tls mode: CustomCertificatecertManager: clusterIssuerName: letsencrypt mode: CertManager-
objectsettings.https.certManager
-
stringsettings.https.certManager.clusterIssuerName
What ClusterIssuer to use for Stronghold.
Currently,
letsencrypt,letsencrypt-staging,selfsignedare available. Also, you can define your own.Default:
letsencrypt
-
-
objectsettings.https.customCertificate
Default:
{}-
stringsettings.https.customCertificate.secretName
The name of the secret in the
d8-systemnamespace to use with Stronghold.This secret must have the kubernetes.io/tls format.
Default:
false
-
-
stringsettings.https.mode
The HTTPS usage mode:
CertManager— Stronghold will use HTTPS and get a certificate from the clusterissuer defined in thecertManager.clusterIssuerNameparameter.CustomCertificate— Stronghold will use HTTPS using the certificate from thed8-systemnamespace.
Default:
CertManagerAllowed values:
CertManager,CustomCertificate
-
-
objectsettings.ingress
Default:
{}-
stringsettings.ingress.class
The class of the Ingress controller used for Stronghold.
An optional parameter. By default, the
modules.ingressClassglobal value is used.Pattern:
^[a-z0-9]([-a-z0-9]*[a-z0-9])?(\.[a-z0-9]([-a-z0-9]*[a-z0-9])?)*$Example:
class: public
-
-
stringsettings.inlet
The way the connection to Stronghold is implemented.
The following inlet types are supported:
Ingress— access via ingress-nginx controller.
Default:
IngressAllowed values:
Ingress -
stringsettings.license
Stronghold EE License key.
Leave empty to use Stronghold CE.
Default:
‘’ -
objectsettings.management
Default:
{}-
array of objectssettings.management.administratorsA list of users and groups that can access Stronghold as administrators. Other authenticated users will access Stronghold with default policy.
Example:
administrators: - name: admins type: Group - name: security type: Group - name: manager@mycompany.tld type: User-
stringsettings.management.administrators.name
-
stringsettings.management.administrators.type
Allowed values:
Group,User
-
-
stringsettings.management.modeEnables Stronghold auto-init and auto-unseal. The root token is stored in the
stronghold-keysSecret.Default:
AutomaticAllowed values:
AutomaticExample:
mode: Automatic
-
-
array of objectssettings.pluginsList of plugins to load into Stronghold. Each plugin is verified by SHA256 checksum.
Example:
plugins: - ignoreFailure: false name: vault-plugin-secrets-github sha256: 72cb1f2775ee2abf12ffb725e469d0377fe7bbb93cd7aaa6921c141eddecab87 url: https://github.com/martinbaillie/vault-plugin-secrets-github/releases/download/v2.3.2/vault-plugin-secrets-github-linux-amd64-
stringsettings.plugins.caPEM-encoded CA certificate(s) used to verify the HTTPS server for this plugin’s URL. If set, only this CA is trusted (not system CAs).
-
booleansettings.plugins.ignoreFailureIf true, failure to download or verify this plugin does not block Stronghold startup, but the plugin functionality will not be available.
Default:
false -
booleansettings.plugins.insecureSkipVerifyIf true, TLS server certificate is not verified for this plugin’s URL.
Default:
false -
stringsettings.plugins.nameFilename of the plugin binary after download.
-
stringsettings.plugins.sha256SHA256 checksum of the file. Download is rejected if the checksum does not match. This will block Stronghold startup unless ignoreFailure is set.
Pattern:
^[a-fA-F0-9]{64}$ -
stringsettings.plugins.urlURL to download the plugin binary (http or https, domain, path and filename). If the file is unavailable, this will block Stronghold startup unless ignoreFailure is set.
Pattern:
^https?://[a-zA-Z0-9][-a-zA-Z0-9.]*[a-zA-Z0-9](/[^/]+)*/[^/.]+$
-
-