The module lifecycle stage: Deprecated
Authentication
By default, the user-authn module is used. Alternatively, authentication can be configured using externalAuthentication.
If neither of these methods is enabled, the dashboard module will be disabled.
The parameters auth.password and accessLevel are no longer supported.
Settings
The module does not have any mandatory parameters.
Requirements
To the Deckhouse version: 1.72 and above.
Parameters
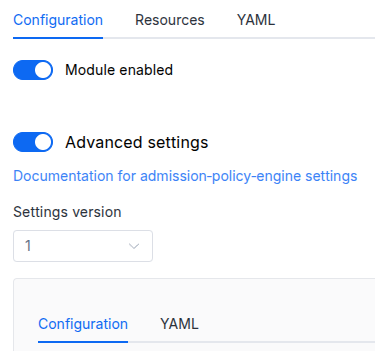
Schema version: 1
-
-
objectsettings.authOptions related to authentication or authorization in the application.
Default:
{}-
array of stringssettings.auth.allowedUserEmails
An array of emails of users that can access module’s public web interfaces.
This parameter is used if the
user-authnmodule is enabled or theexternalAuthenticationparameter is set. -
array of stringssettings.auth.allowedUserGroups
An array of user groups that can access the dashboard.
This parameter is used if the
user-authnmodule is enabled or theexternalAuthenticationparameter is set.Warning. Note that you must add those groups to the appropriate field in the DexProvider config if this module is used together with the user-authn one.
-
objectsettings.auth.externalAuthentication
Parameters to enable external authentication based on the Ingress NGINX external-auth mechanism that uses the Nginx auth_request module.
External authentication is enabled automatically if the user-authn module is enabled.
Warning. For security reasons, this mode only works if
https.mode(global or for a module) is not set toDisabled.-
stringsettings.auth.externalAuthentication.authSignInURLThe URL to redirect the user for authentication (if the authentication service returned a non-200 HTTP response code).
-
stringsettings.auth.externalAuthentication.authURLThe URL of the authentication service. If the user is authenticated, the service should return an HTTP 200 response code.
-
booleansettings.auth.externalAuthentication.useBearerTokensThe dashboard must use the user ID to work with the Kubernetes API (the authentication service must return the Authorization HTTP header that contains the bearer-token – the dashboard will use this token to make requests to the Kubernetes API server).
Default:
false
-
-
array of stringssettings.auth.whitelistSourceRangesThe CIDR range for which authentication to access the dashboard is allowed.
Example:
whitelistSourceRanges: - 1.1.1.1/32
-
-
booleansettings.highAvailability
Manually enable the high availability mode.
By default, Deckhouse automatically decides whether to enable the HA mode. Click here to learn more about the HA mode for modules.
Example:
highAvailability: true -
objectsettings.https
What certificate type to use with the dashboard.
This parameter completely overrides the
global.modules.httpssettings.Examples:
customCertificate: secretName: foobar mode: CustomCertificatecertManager: clusterIssuerName: letsencrypt mode: CertManager-
objectsettings.https.certManager
-
stringsettings.https.certManager.clusterIssuerNameWhat ClusterIssuer to use for the dashboard. Currently,
letsencrypt,letsencrypt-staging,selfsignedare available; also, you can define your own.Default:
letsencrypt
-
-
objectsettings.https.customCertificate
-
stringsettings.https.customCertificate.secretNameThe name of the Secret in the
d8-systemnamespace to use with the dashboard (this Secret must have the kubernetes.io/tls format).Default:
false
-
-
stringsettings.https.mode
The HTTPS usage mode:
CertManager— the dashboard will use HTTPS and get a certificate from the ClusterIssuer defined in thecertManager.clusterIssuerNameparameter;CustomCertificate— the dashboard will use the certificate from thed8-systemnamespace for HTTPS;Disabled— dashboard will not work in this mode;OnlyInURI— the dashboard will work over HTTP (thinking that there is an external HTTPS load balancer in front of it that terminates HTTPS traffic). All the links in the user-authn will be generated using the HTTPS scheme. Load balancer should provide a redirect from HTTP to HTTPS.
Allowed values:
Disabled,CertManager,CustomCertificate,OnlyInURI
-
-
stringsettings.ingressClass
The class of the Ingress controller used for the dashboard.
By default, the
modules.ingressClassglobal value is used.Pattern:
^[a-z0-9]([-a-z0-9]*[a-z0-9])?(\.[a-z0-9]([-a-z0-9]*[a-z0-9])?)*$ -
objectsettings.nodeSelector
The same as in the Pods’
spec.nodeSelectorparameter in Kubernetes.If the parameter is omitted or
false, it will be determined automatically. -
array of objectssettings.tolerations
The same as in the Pods’
spec.tolerationsparameter in Kubernetes.If the parameter is omitted or
false, it will be determined automatically.-
stringsettings.tolerations.effect
-
stringsettings.tolerations.key
-
stringsettings.tolerations.operator
-
integersettings.tolerations.tolerationSeconds
-
stringsettings.tolerations.value
-
-