Available with limitations in: CE, BE, SE, SE+
Available without limitations in: EE
The module lifecycle stage: General Availability
The module has 4 alerts.
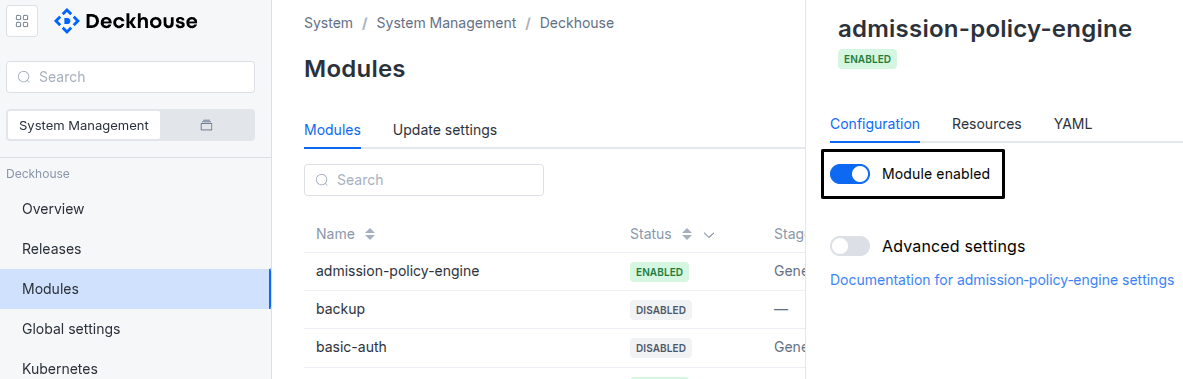
The module is enabled by default in the following bundles: Default, Managed.
The module is disabled by default in the Minimal bundle.
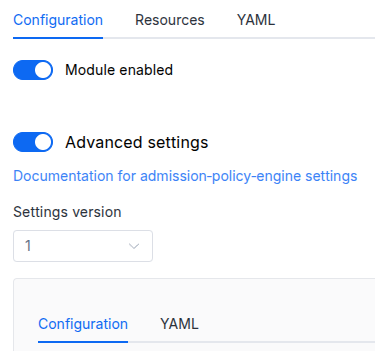
Parameters
Schema version: 1
- objectsettings
- objectsettings.denyVulnerableImages
Available in editions: EE
Trivy provider settings.
The Trivy provider prevents creation of the Pod, Deployment, StatefulSet, and DaemonSet resources with images containing vulnerabilities in namespaces labeled with
security.deckhouse.io/trivy-provider: "".- array of stringssettings.denyVulnerableImages.allowedSeverityLevels
List of allowed vulnerability severity levels.
Images containing only vulnerabilities of the specified severity levels will not be blocked.
- stringElement of the array
Allowed values:
UNKNOWN,LOW,MEDIUM,HIGH,CRITICAL
- booleansettings.denyVulnerableImages.enabled
Enable the Trivy provider.
Default:
false - array of objectssettings.denyVulnerableImages.registrySecrets
List of additional Secrets for accessing private registries.
By default, the
deckhouse-registrySecret is used to download images for scanning.Default:
[]- stringsettings.denyVulnerableImages.registrySecrets.name
Required value
- stringsettings.denyVulnerableImages.registrySecrets.namespace
Required value
- stringsettings.denyVulnerableImages.storageClass
Name of the StorageClass used by the Trivy provider.
If the value is not specified, the StorageClass set in the global
settings.modules.storageClassparameter is used instead.The global
settings.modules.storageClassparameter is only applied when the module is enabled. Changing the global parameter while the module is enabled will not trigger disk re-provisioning.Warning. If you specify a value different from the current StorageClass used in the existing PersistentVolumeClaim, the disk will be re-provisioned, and all data will be deleted.
If you set it to
false,emptyDirwill be forcibly used instead of a PVC.Examples:
storageClass: ceph-ssdstorageClass: 'false'
- objectsettings.podSecurityStandards
Pod Security Standards policy settings (PSS).
- stringsettings.podSecurityStandards.defaultPolicy
Sets the default Pod Security Standards policy for all non-system namespaces:
Privileged— an unrestricted policy. Privilege escalation is possible with this policy;Baseline— a policy with minimum restrictions that prevents privilege escalation;Restricted— a policy with maximum restrictions that conforms to current best practices for securely running applications in a cluster.
By default:
Baseline— if a Deckhouse version starting with v1.55 is being installed;Privileged— if a Deckhouse version lower than v1.55 is being installed (upgrading Deckhouse in a cluster to v1.55+ does not automatically result in a default policy change).
Allowed values:
Privileged,Baseline,Restricted - stringsettings.podSecurityStandards.enforcementAction
The enforcement action to control what to do with the result of the constraint.
- Deny — Deny action.
- Dryrun — No action. It is used when debugging. Information about the event can be viewed in Grafana or in the console via kubectl.
- Warn — Same as
Dryrun. In addition to the event information, it provides some info on why that constraint would have been denied if you had setDenyinstead ofWarn.
Default:
DenyAllowed values:
Warn,Deny,Dryrun - objectsettings.podSecurityStandards.policies
Sets additional policy parameters.
- objectsettings.podSecurityStandards.policies.hostPorts
HostPort constraint settings.
- array of objectssettings.podSecurityStandards.policies.hostPorts.knownRanges
Set the range of known ports which will be allowed in a hostPort binding.
- integersettings.podSecurityStandards.policies.hostPorts.knownRanges.max
- integersettings.podSecurityStandards.policies.hostPorts.knownRanges.min