Available with limitations in: CE
Available without limitations in: BE, SE, SE+, EE
The module lifecycle stage: General Availability
Caution! We strongly do not recommend creating Pods and ReplicaSets – these objects are secondary and should be created by other controllers. Access to creating and modifying Pods and ReplicaSets is disabled.
Caution! Currently, the multi-tenancy mode (namespace-based authorization) is implemented according to a temporary scheme and isn’t guaranteed to be entirely safe and secure! The
allowAccessToSystemNamespaces,namespaceSelectorandlimitNamespacesoptions in the custom resource will no longer be applied if the authorization system’s webhook is unavailable for some reason. As a result, users will have access to all namespaces. After the webhook availability is restored, the options will become relevant again.
All access rights are configured using Custom Resources.
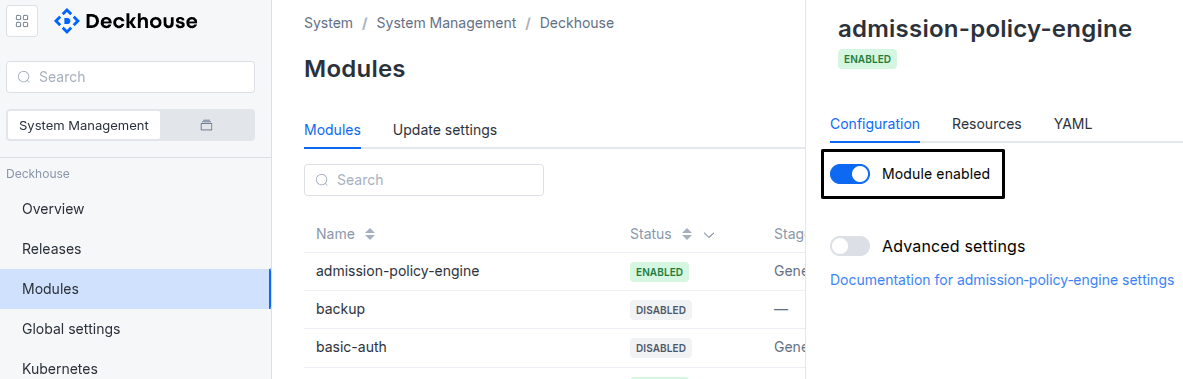
The module is enabled by default in the following bundles: Default, Managed.
The module is disabled by default in the Minimal bundle.
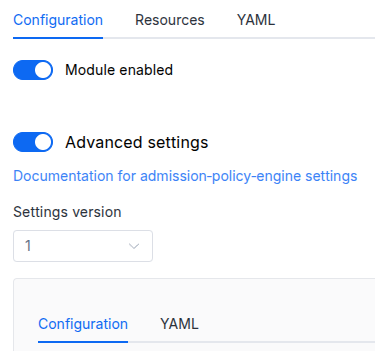
Parameters
Schema version: 1
- objectsettings
- booleansettings.controlPlaneConfigurator.enabled
Passes parameters for configuring
authz-webhookto thecontrol-plane-managermodule (see the parameters of the control-plane-manager module).If this parameter is disabled, the
control-plane-managermodule assumes that Webhook-based authorization is disabled by default. In this case (if no additional settings are provided), thecontrol-plane-managermodule will try to delete all references to the Webhook plugin from the manifest (even if you configure the manifest manually).Default:
trueExamples:
enabled: trueenabled: false
- booleansettings.enableMultiTenancy
Available in editions: BE, SE, SE+, EE
Enable namespace-based authorization (multi-tenancy mode).
All the
kube-apiserversettings required for namespace-based authorization are performed automatically by the control-plane-manager module (more details).Default:
falseExamples:
enableMultiTenancy: trueenableMultiTenancy: false