Available in: EE
The module lifecycle stage: General Availability
The module has requirements for installation
Requirements
To the Deckhouse version: 1.75 and above.
Parameters
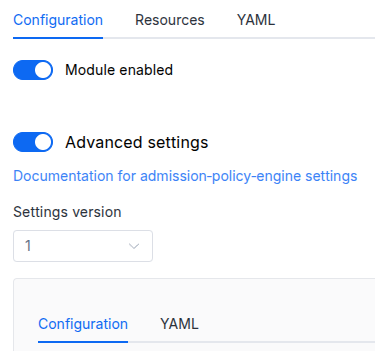
Schema version: 1
-
-
array of objectssettings.additionalRegistryCA
List of registry CA certificates for connecting to private registries.
If it is necessary to specify a certificate with an intermediate certificate, the chain is specified without additional line breaks.
Example:
additionalRegistryCA: - name: example CA ca: | -----BEGIN CERTIFICATE----- ................. -----END CERTIFICATE----- - name: CA with intermediate CA ca: | -----BEGIN CERTIFICATE----- ................. -----END CERTIFICATE----- -----BEGIN CERTIFICATE----- ................. -----END CERTIFICATE------
stringsettings.additionalRegistryCA.ca
-
stringsettings.additionalRegistryCA.name
-
-
array of stringssettings.additionalVulnerabilityReportFieldsA list of additional fields from the vulnerability database to add to the VulnerabilityReport.
Example:
additionalVulnerabilityReportFields: - Class - Target -
integersettings.concurrentScanJobsLimitMaximum number of scan jobs that the operator can run concurrently.
Default:
10Allowed values:
1 <= XExamples:
concurrentScanJobsLimit: 3concurrentScanJobsLimit: 5concurrentScanJobsLimit: 10 -
objectsettings.denyVulnerableImages
Settings to prohibit the creation of
Pod/Deployment/StatefulSet/DaemonSetwith vulnerable images in namespaces labeledsecurity.deckhouse.io/trivy-provider: "".Note: This constraint is enforced only during admission (resource creation/update). Gatekeeper audit does not evaluate this constraint.
Default:
{}-
array of stringssettings.denyVulnerableImages.allowedSeverityLevelsImages containing only vulnerabilities of specified severities will not be denied.
-
stringsettings.denyVulnerableImages.allowedSeverityLevels.Element of the array
Allowed values:
UNKNOWN,LOW,MEDIUM,HIGH,CRITICAL
-
-
booleansettings.denyVulnerableImages.enabledDeny use of vulnerable images in cluster namespaces labeled as
security.deckhouse.io/trivy-provider: "".Default:
false -
array of objectssettings.denyVulnerableImages.registrySecrets
List of additional registry secrets to use for downloading images from private registries.
By default, the
deckhouse-registrysecret is used to download images for scanning.Default:
[]-
stringsettings.denyVulnerableImages.registrySecrets.name
-
stringsettings.denyVulnerableImages.registrySecrets.namespace
-
-
-
booleansettings.disableSBOMGeneration
Disables SBOM reports generation.
Warning. When this options is set to true, all current SBOM reports are deleted from the cluster (the cleanup is executed only once).
Default:
falseExamples:
disableSBOMGeneration: truedisableSBOMGeneration: false -
booleansettings.insecureDbRegistryAllows Trivy to download vulnerability databases using insecure HTTPS connections (not passed TLS certificate verification) or HTTP connections.
Default:
falseExamples:
insecureDbRegistry: trueinsecureDbRegistry: false -
array of stringssettings.insecureRegistriesList of container registry addresses to which insecure HTTPS connections (not passed TLS certificate verification) or HTTP connections are allowed.
Example:
insecureRegistries: - my.registry.com - http-only.registry.io -
booleansettings.linkCVEtoBDUConverts CVE database vulnerability records to BDU (FSTEC Russia) database records.
Default:
falseExamples:
linkCVEtoBDU: truelinkCVEtoBDU: false -
objectsettings.nodeScanningConfiguration for node (host filesystem) vulnerability scanning. This feature scans the host filesystem of each Kubernetes node to detect OS package vulnerabilities.
Default:
{}-
integersettings.nodeScanning.concurrentLimitMaximum number of concurrent node scan jobs.
Default:
1Allowed values:
1 <= XExamples:
concurrentLimit: 1concurrentLimit: 2concurrentLimit: 3 -
booleansettings.nodeScanning.enabled
Enables node vulnerability scanning.
When enabled, the operator will scan the host filesystem of each node for OS package vulnerabilities.
Default:
falseExamples:
enabled: trueenabled: false -
booleansettings.nodeScanning.hideUnfixedCVEs
When true, only report vulnerabilities that have a fix available.
This significantly reduces report size but hides unfixed vulnerabilities.
Default:
falseExamples:
hideUnfixedCVEs: truehideUnfixedCVEs: false -
objectsettings.nodeScanning.nodeSelectorFilter nodes by labels. Only nodes matching all labels will be scanned.
Default:
{}Examples:
node-role.kubernetes.io/worker: ""env: production -
array of stringssettings.nodeScanning.pkgTypes
List of package types to scan:
os— OS packages;library— application libraries.
Default:
[ "os" ]Examples:
pkgTypes: - ospkgTypes: - os - library-
stringsettings.nodeScanning.pkgTypes.Element of the array
Allowed values:
os,library
-
array of stringssettings.nodeScanning.scanners
List of scanners to use for node scanning:
vuln— vulnerability scanner;secret— secret scanner.
Default:
[ "vuln" ]Examples:
scanners: - vulnscanners: - vuln - secret-
stringsettings.nodeScanning.scanners.Element of the array
Allowed values:
vuln,secret
-
array of stringssettings.nodeScanning.severities
Filter vulnerabilities by severity.
Warning. Without filtering, reports can exceed etcd’s 3MB object size limit on nodes with many packages.
Default:
[ "CRITICAL", "HIGH" ]Examples:
severities: - CRITICAL - HIGHseverities: - CRITICAL - HIGH - MEDIUM-
stringsettings.nodeScanning.severities.Element of the array
Allowed values:
UNKNOWN,LOW,MEDIUM,HIGH,CRITICAL
-
-
array of stringssettings.nodeScanning.skipDirs
List of directories to skip during node scanning.
By default, container runtime directories and virtual filesystems are excluded.
Default:
[ "/proc", "/sys", "/dev", "/run", "/var/lib/containerd", "/var/lib/docker", "/var/lib/kubelet/pods" ]Example:
skipDirs: - /proc - /sys - /dev -
stringsettings.nodeScanning.timeout
Timeout for node scan jobs.
If not set, the default scan job timeout is used.
Default:
Examples:
timeout: 10mtimeout: 30m
-
-
objectsettings.nodeSelector
Optional
nodeSelectorforoperator-trivyand scan jobs.The same as
spec.nodeSelectorfor the Kubernetes pod.If the parameter is omitted or
false, it will be determined automatically.Example:
disktype: ssd -
array of stringssettings.reportResourceLabels
A list of additional labels for marking Trivy’s reports (VulnerabilityReport).
The values of these labels will correspond to the values of the scanned resources’ labels.
Examples:
reportResourceLabels: appreportResourceLabels: env -
objectsettings.scanJobResources
Resource
requests/limitsfor scan jobs (ScanJobpods).If the parameter is omitted, the module uses the default values (as it did before this setting existed). If the parameter is specified, you may set only some of the fields (e.g. only memory) — unspecified fields will not be forced by the module.
Default:
{}Example:
limits: cpu: 500m memory: 500M requests: cpu: 100m memory: 100M-
objectsettings.scanJobResources.limits
Default:
{}-
stringsettings.scanJobResources.limits.cpu
Examples:
cpu: 500mcpu: "1" -
stringsettings.scanJobResources.limits.memory
Examples:
memory: 500Mmemory: 1Gi
-
-
objectsettings.scanJobResources.requests
Default:
{}-
stringsettings.scanJobResources.requests.cpu
Examples:
cpu: 100mcpu: 250m -
stringsettings.scanJobResources.requests.memory
Examples:
memory: 100Mmemory: 256Mi
-
-
-
array of stringssettings.severitiesFilter vulnerability reports by their severities.
Examples:
severities: - CRITICAL - HIGH - MEDIUM - LOW - UNKNOWNseverities: - CRITICAL - HIGH-
stringsettings.severities.Element of the array
Allowed values:
UNKNOWN,LOW,MEDIUM,HIGH,CRITICAL
-
-
stringsettings.storageClass
The name of StorageClass that will be used in the cluster by default.
If the value is not specified, the StorageClass will be used according to the global storageClass parameter setting.
The global
storageClassparameter is only considered when the module is enabled. Changing the globalstorageClassparameter while the module is enabled will not trigger disk re-provisioning.Warning. Specifying a value different from the one currently used (in the existing PVC) will result in disk re-provisioning and all data will be deleted.
If
falseis specified,emptyDirwill be forced to be used.Examples:
storageClass: ceph-ssdstorageClass: "false" -
array of objectssettings.tolerations
Optional
tolerationsforoperator-trivyand scan jobs.The same as
spec.tolerationsfor the Kubernetes pod.If the parameter is omitted or
false, it will be determined automatically.Example:
effect: NoSchedule key: key1 operator: Equal value: value1-
stringsettings.tolerations.effect
-
stringsettings.tolerations.key
-
stringsettings.tolerations.operator
-
integersettings.tolerations.tolerationSeconds
-
stringsettings.tolerations.value
-
-
booleansettings.useVEXFromOCISearch OCI registry for VEX Attestations of scanned images and suppress reporting of vulnerabilities declared in them.
Default:
trueExamples:
useVEXFromOCI: trueuseVEXFromOCI: false
-