Available with limitations in: CE, BE
Available without limitations in: SE, SE+, EE
The module lifecycle stage: General Availability
The module has requirements for installation
Requirements
To the Deckhouse version: 1.71 and above.
Parameters
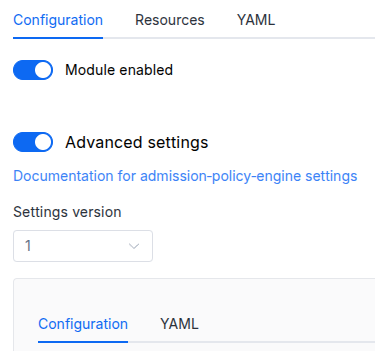
Schema version: 1
-
-
booleansettings.allowAnyoneToRuleTheClusterDeprecatedThis parameter is ignored. It will be removed in future releases. It was used to skip user permissions, so any user would have highest possible privileges in the UI.
Default:
false -
objectsettings.authAuthentication configuration.
Default:
{}-
array of stringssettings.auth.allowedUserGroups
An array of user groups that can access the web UI.
This parameter is used if the user-authn module is enabled or the
externalAuthenticationparameter is set.Caution! Note that you must add those groups to the appropriate field in the DexProvider config if this module is used together with the user-authn one.
-
objectsettings.auth.externalAuthenticationParameters to enable external authentication. Uses Nginx Ingress external-auth mechanism which is based on the the Nginx auth_request module.
-
stringsettings.auth.externalAuthentication.authSignInURLURL to redirect the user for authentication (if the authentication service returned a non-200 HTTP response code).
-
stringsettings.auth.externalAuthentication.authURLURL of the authentication service. If the user is authenticated, the service should return an HTTP 200 response code.
-
booleansettings.auth.externalAuthentication.useBearerTokens
The console must use the user ID to work with the Kubernetes API (the authentication service must return the Authorization HTTP header that contains the bearer-token – the console will use this token to make requests to the Kubernetes API server).
Default value is
true.Caution! For security reasons, this mode only works if
https.mode(global or for a module) is not set toDisabled.
-
-
stringsettings.auth.passwordDeprecated
This parameter is ignored and will be removed in future releases.
It was used for http authorization of the
adminuser, if the user-authn module was disabled or theexternalAuthenticationparameter was not set.Now the external authentication is required for module to function properly.
-
stringsettings.auth.sessionTTL
User session will be kept for specified amount of time even if user will not log in.
Specified with
s,morhsuffix.Default:
24h -
array of stringssettings.auth.whitelistSourceRangesAn array if CIDRs that are allowed to authenticate.
Example:
whitelistSourceRanges: - 1.1.1.1/32
-
-
integersettings.externalWebsocketPortExternal port for WebSocket protocol requests. If WebSocket traffic goes through a proxy server before reaching the backend, the frontend application will use this to connect to the proxy server.
Allowed values:
1 <= X <= 65535 -
booleansettings.highAvailability
Manually enable the high availability mode.
By default, Deckhouse automatically decides whether to enable the HA mode. Click here to learn more about the HA mode for modules.
Examples:
highAvailability: truehighAvailability: false -
objectsettings.https
What certificate type to use with frontend and status apps.
This parameter completely overrides the
global.modules.httpssettings.Examples:
customCertificate: secretName: foobar mode: CustomCertificatecertManager: clusterIssuerName: letsencrypt mode: CertManager-
objectsettings.https.certManager
-
stringsettings.https.certManager.clusterIssuerName
What ClusterIssuer to use for frontend.
Currently,
letsencrypt,letsencrypt-staging,selfsignedare available. Also, you can define your own.Default:
letsencrypt
-
-
objectsettings.https.customCertificate
Default:
{}-
stringsettings.https.customCertificate.secretName
The name of the secret in the
d8-systemnamespace to use with frontend.This secret must have the kubernetes.io/tls format.
Default:
false
-
-
stringsettings.https.mode
The HTTPS usage mode:
Disabled— in this mode, the web UI can only be accessed over HTTP. Caution! This mode is not supported. HTTPS is required for the module to function properly. If HTTPS is disabled, the web UI will be unavailable.CertManager— frontend will use HTTPS and get a certificate from the clusterissuer defined in thecertManager.clusterIssuerNameparameter.CustomCertificate— frontend will use HTTPS using the certificate from thed8-systemnamespace.OnlyInURI— frontend will work over HTTP (thinking that there is an external HTTPS load balancer in front that terminates HTTPS traffic). All the links in theuser-authnwill be generated using the HTTPS scheme.
Allowed values:
Disabled,CertManager,CustomCertificate,OnlyInURI
-
-
stringsettings.ingressClass
The class of the Ingress controller used for the web UI.
An optional parameter. By default, the
modules.ingressClassglobal value is used.Pattern:
^[a-z0-9]([-a-z0-9]*[a-z0-9])?(\.[a-z0-9]([-a-z0-9]*[a-z0-9])?)*$Example:
ingressClass: nginx -
objectsettings.nodeSelector
Node selector for frontend and backend pods. The same as in the Pods’
spec.nodeSelectorparameter in Kubernetes.If the parameter is omitted or
false, it will be determined automatically.Example:
disktype: ssd -
array of objectssettings.tolerations
Node tolerations for frontend and backend pods. The same as in the Pods’
spec.tolerationsparameter in Kubernetes;If the parameter is omitted or
false, it will be determined automatically.Example:
tolerations: - effect: NoSchedule key: key1 operator: Equal value: value1-
stringsettings.tolerations.effect
-
stringsettings.tolerations.key
-
stringsettings.tolerations.operator
-
integersettings.tolerations.tolerationSeconds
-
stringsettings.tolerations.value
-
-