Available with limitations in: CE, BE, SE
Available without limitations in: SE+, EE
The module lifecycle stage: General Availability
The cni-cilium module provides a network in a cluster. It is based on the Cilium project.
Limitations
- Services with type
NodePortandLoadBalancerare incompatible with hostNetwork endpoints in LB modeDSR. Switch toSNATmode if it is required. HostPortpods only bind to one IP address. If the OS has multiple interfaces/IP, Cilium will choose one, preferringprivatetopublic.- To ensure the stable operation of
cni-ciliumon cluster nodes, disable Elastic Agent or restrict its access to the Elastic management server. Elastic Agent includes an Elastic Endpoint component which uses the Extended Berkeley Packet Filter (eBPF) technology on cluster nodes and may remove critical eBPF programs required forcni-ciliumto work correctly. For detailed information and discussion of the issue, refer to the publications of the Cilium and Elastic projects. - Kernel requirements:
- Linux kernel version not lower than
5.8for thecni-ciliummodule to work and work together with the istio, openvpn or node-local-dns modules.
- Linux kernel version not lower than
- OS compatibility:
- Ubuntu:
- incompatible with version 18.04;
- HWE kernel installation required for working with version 20.04.
- Astra Linux:
- incompatible with the “Smolensk” edition.
- CentOS:
- for versions 7 and 8, a new kernel from the repository is required.
- Ubuntu:
Handling external traffic in different bpfLB modes (replacing kube-proxy from Cilium)
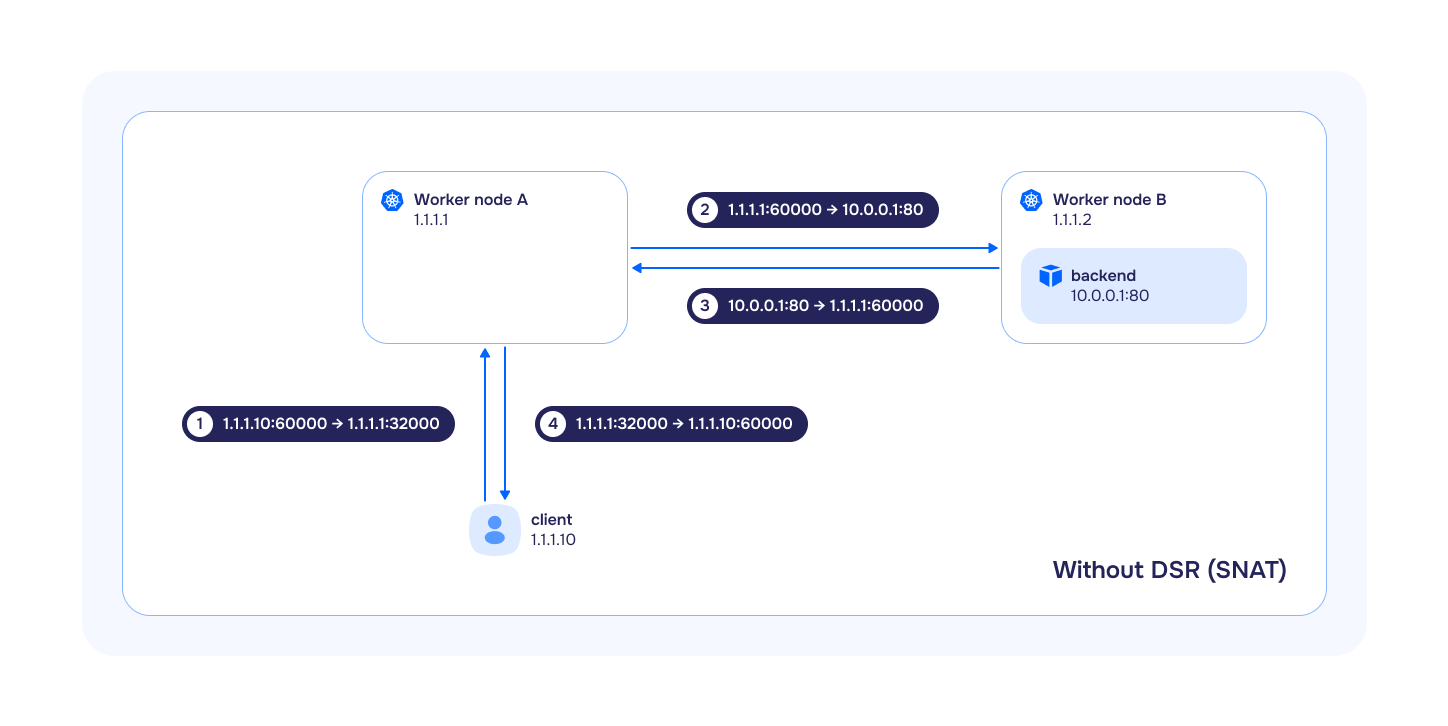
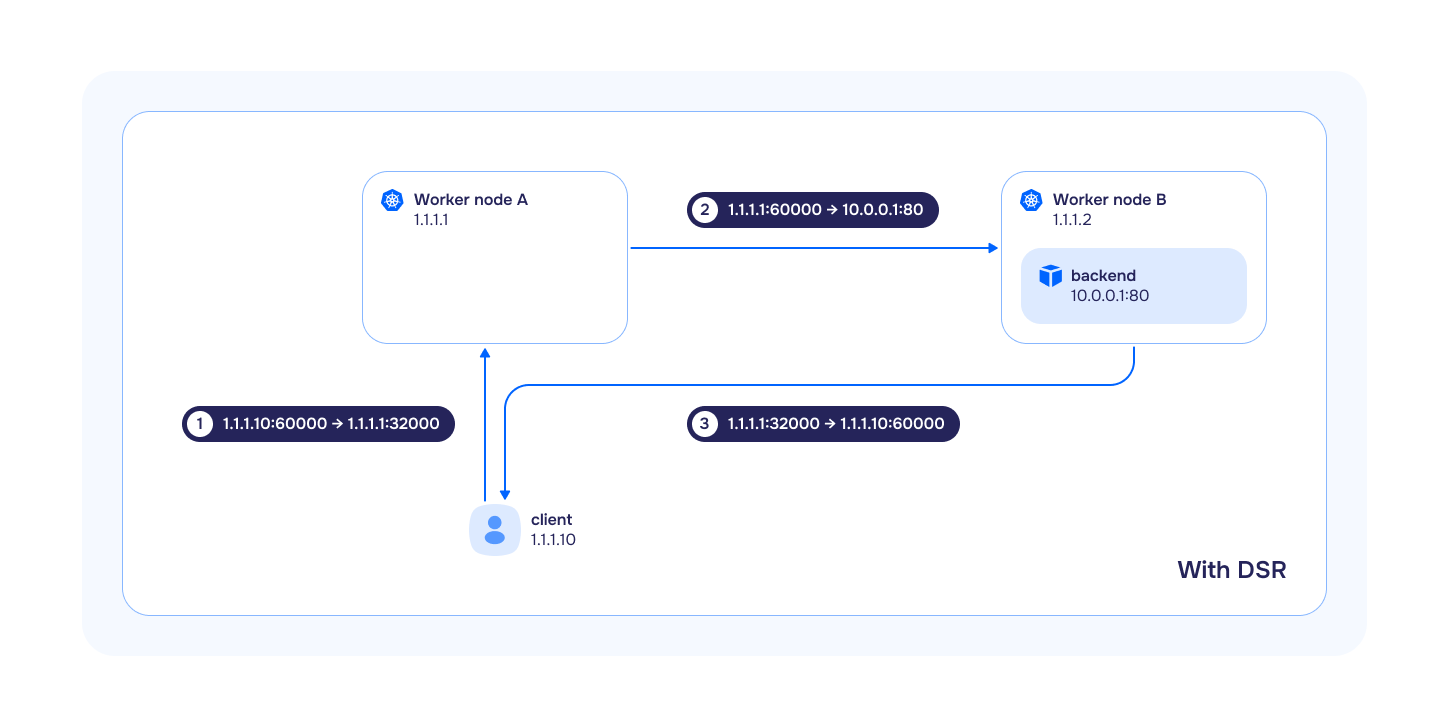
Kubernetes typically uses schemes where traffic comes to a balancer that distributes it among many servers. Both incoming and outgoing traffic passes through the balancer. Thus, the total throughput is limited by the resources and channel width of the balancer. To optimize traffic and unload the balancer, the DSR mechanism was invented, in which incoming packets go through the balancer, and outgoing ones go directly from the terminating servers. Since responses are usually much larger in size than requests, this approach can significantly increase the overall throughput of the scheme.
To extend the capabilities, the module allows selectable mode of operation, which affects the behavior of Service with the NodePort and LoadBalancer types:
SNAT(Source Network Address Translation) — is a subtype of NAT in which, for each outgoing packet, the source IP address is translated to the IP address of the gateway from the target subnet, and incoming packets passing through the gateway are translated back based on a translation table. In this mode,bpfLBfully replicates the logic ofkube-proxy:- if
externalTrafficPolicy: Localis specified in theService, the traffic will be forwarded and balanced only to those target pods running on the same node where the traffic arrived. If the target pod is not running on this node, the traffic will be dropped. - if
externalTrafficPolicy: Clusteris specified in theService, the traffic will be forwarded and balanced to all target pods in the cluster. At the same time, if the target pods are located on other nodes, SNAT will be performed when transmitting traffic to them (the source IP address will be replaced with the InternalIP of the node).
- if
DSR(Direct Server Return) — is a method where all incoming traffic passes through the load balancer, and all outgoing traffic bypasses it. This method is used instead ofSNAT. Often, responses are much larger than requests, andDSRcan significantly increase the overall throughput of the scheme:- if
externalTrafficPolicy: Localis specified in theService, its behavior is completely analogous tokube-proxyandbpfLBinSNATmode. - if
externalTrafficPolicy: Clusteris specified in theService, the traffic will be forwarded and balanced to all target pods in the cluster. It is important to take into account the following features:- if the target pods are on other nodes, then the source IP address will be preserved when incoming traffic is sent to them;
- outgoing traffic will go directly from the node on which the target pod was launched;
- the source IP address will be replaced with the external IP address of the node to which the incoming request originally came.
- if
In case of using DSR and Service mode with externalTrafficPolicy: Cluster additional network environment settings are required. Network equipment must be ready for asymmetric traffic flow: IP address anti-spoofing tools (uRPF, sourceGuard, etc.) must be disabled or configured accordingly.
Hybrid— in this mode, TCP traffic is processed inDSRmode, and UDP inSNATmode.
Using CiliumClusterwideNetworkPolicies
Using CiliumClusterwideNetworkPolicies if the policyAuditMode option is absent in the cni-cilium module settings may lead to incorrect operation of Control plane or loss of SSH access to all cluster nodes.
Follow these steps to use CiliumClusterwideNetworkPolicies:
-
Apply the primary set of
CiliumClusterwideNetworkPolicyobjects. To do this, in the settings of the cni-cilium module add the configuration optionpolicyAuditModewith the valuetrue. The option can be removed after applying allCiliumClusterwideNetworkPolicyobjects and verifying their functionality in Hubble UI. -
Apply network security policy rule:
apiVersion: "cilium.io/v2" kind: CiliumClusterwideNetworkPolicy metadata: name: "allow-control-plane-connectivity" spec: ingress: - fromEntities: - kube-apiserver nodeSelector: matchLabels: node-role.kubernetes.io/control-plane: ""
If CiliumClusterwideNetworkPolicies are not used, the control plane may work incorrectly for up to a minute during the reboot of cilium-agent pods. This occurs due to Conntrack table reset. Binding to the kube-apiserver entity helps to bypass the bug.
Changing Cilium Operation Mode
When changing Cilium’s operation mode (the tunnelMode parameter) from Disabled to VXLAN or vice versa, it is necessary to reboot all nodes, otherwise, pod availability issues may occur.
Disabling the kube-proxy Module
Cilium fully replaces the functionality of the kube-proxy module, so kube-proxy is automatically disabled when the cni-cilium module is enabled.
Using selective load balancing algorithm for services
In Deckhouse Kubernetes Platform, you can apply the following algorithms to load balance service traffic:
Random: Randomly select a backend for each connection. Easy to implement, but does not always provide even distribution.Maglev: Uses consistent hashing to distribute traffic evenly, suitable for large-scale services.Least Connections: Directs traffic to the backend with the lowest number of active connections, optimizing load for applications with long-lived connections.
By default, the Random balancing algorithm is set for all services. However, Deckhouse allows you to override the algorithm for individual services. To use a selective balancing algorithm for a specific service, follow these steps:
- Edit the
cni-ciliummodule configuration in Deckhouse by enabling theextraLoadBalancerAlgorithmsEnabledparameter. This activates support for service annotations for selective algorithms. - In the service manifest, specify the
service.cilium.io/lb-algorithmannotation with one of the values:random,maglev, orleast-conn.
This mechanism requires Linux kernel version 5.15 or higher to work correctly.
Using Egress Gateway
The feature is available only in the following Deckhouse Kubernetes Platform editions: SE+, EE.
Egress Gateway in Deckhouse Kubernetes Platform can be used in one of two modes: Basic and Mode with Virtual IP. Use Custom Resource EgressGateway (parameter spec.sourceIP.node) to select the mode.
Basic mode
Pre-configured IP addresses are used on egress nodes.
Virtual IP mode
The ability to dynamically assign additional IP addresses to nodes is implemented.
Exporting data from Hubble
Deckhouse Kubernetes Platform allows to configure data export from Hubble running inside Cilium agents using the cluster-scoped custom resource HubbleMonitoringConfig.
To enable export, create a HubbleMonitoringConfig resource.
Creating or modifying the HubbleMonitoringConfig resource will restart all Cilium agents in the cluster.
Third-party components
List of third-party software used in the cni-cilium module:
-
License: Apache License 2.0
Cilium is open source software for providing and transparently securing network connectivity and loadbalancing between application workloads such as application containers or processes.